Muss sagen das nervt mich ja schon ganz schön das die Amis das Video Portal
haben, war mit dem PC mal in dem Video Portal drin und muss sagen was dort an Content
ist, ist echt nicht übel. Also es sind auch sehr viele Serien die mann sich anschauen kann
wo mann sagen kann das würde sich ja richtig lohnen.
Jetzt hat ein findiger Typ aus GB sich mal dran gesetzt und mal ein wenig getüftelt wie mann denn
aus Europa auf das Portal kommt. Das ganze ist schon ein bisschen Tricky - oder auch nicht
Vorraussetzung ist halt ein Server in den Staaten oder wenn mann jemand kennen sollte mit schnellem Rechner sollte es auch so gehen, will das ganze hier mal posten, vielleicht hätten ja auch
mehere Leute Interesse da dran was in der Art zu realisieren.
Ist ein Server in den Staaten mieten eigentlich teuer ????
Vielleicht sponsort ja jemand sowas fürs Board, wäre ja echt mal was besonderes wenn mann
seinen User sowas anbieten könnte.
Oder wir legen zusammen sind jetzt nur mal Vorschläge meiner Seite !!!
Na ja waren jetzt mal so paar Gedankengänge von mir, vielleicht hat ja noch jemand eine
bessere Idee, dafür soll der Thread ja da sein !!!
Hier mal die Daten wie der Brite das angestellt hat:
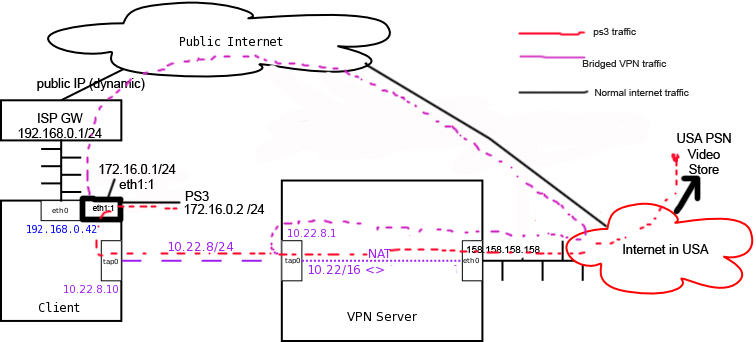
The Technical Details :-
Whats needed:-
1 USA host capable of using OpenVPN and the TAP interface.
1 NON User client capable of OpenVPN and the TAP interface.
OpenSSL for making and signing certificates and becoming a CA.
The ability to configure NAT. I use iptables in this example.
My example is based on using Linux servers. This will also work for a Windows environment but I dont know what tools you would use in place of iptables.
The Server Configuration :-
mkdir -p /etc/openvpn/gateway # you can replace gateway with whatever directory name you want to use.
cd # go back to your root home directory
# easy-rsa is available under /usr/share/openvpn/easy-rsa
vi /etc/conf.d/local.start # to add echo 1 > /proc/sys/net/ipv4/ip_forward
Windows XP Client
Install openvpn-2.0-install.exe
Install OpenVPN GUI [optional]
Configuration
OpenVPN server configuration file (/etc/openvpn/gateway/local.conf)
Code:
port 1194
dev tap
tls-server
cd /etc/openvpn/gateway
ca ca.crt
cert gateway.crt
key gateway.key
dh dh1024.pem
tls-auth ta.key 0
mode server
duplicate-cn
ifconfig 10.22.8.1 255.255.255.0
ifconfig-pool 10.22.8.10 10.22.8.15 255.255.255.0
push “route-gateway 10.22.8.1″
mtu-test
tun-mtu 1500
tun-mtu-extra 32
mssfix 1450
ping 10
ping-restart 120
push “ping 10″
push “ping-restart 60″
push “route 10.22.8.0 255.255.255.0 10.22.8.1″
comp-lzo
log-append /var/log/openvpn.log
verb 4
OpenVPN Linux client configuration (/etc/openvpn/client/local.conf)
vi /etc/conf.d/local.start # to add echo 1 > /proc/sys/net/ipv4/ip_forward
Windows XP Client
Install openvpn-2.0-install.exe
Install OpenVPN GUI [optional]
Copy local.conf to the correct folder.
Use the linux client local.conf below.
Linux Client
Code:
port 1194
dev tap
remote vpnserverpublicipaddress
float
tls-client
cd /etc/openvpn/client <—remove for windows
ca ca.crt
cert client.crt
key client.key
tls-auth ta.key 1
mtu-test
tun-mtu 1500
tun-mtu-extra 32
mssfix 1450
pull
comp-lzo
log-append /var/log/openvpn.log <–change path for windows
verb 4
Symbolic linked the configuration files for Linux (server/client)
Code:
cd /etc/openvpn
# foreach sub-directory, we create a symbolic link to the local.conf to the current directory since the new init script don’t scan for sub-directory
# anymore instead it looks for .conf files. With the sample environment defined above, we have:
ln -s gateway/local.conf gateway.conf
Now to create the SSL Certificates
For Setting up your own Certificate Authority (CA) and generating certificates and keys for an OpenVPN server and multiple clients you could follow http://openvpn.net/index.php/documentation/howto.html#pki
or here is how I did it.
Code:
openvpn –genkey –secret ta.key
Then I basically copy this file to server and all clients machines via secure channel.
To generate the server certificate and key file for /etc/openvpn/gateway.
Code:
cd ~easy-rsa
vi vars # update the KEY_COUNTRY, KEY_PROVINCE, KEY_CITY, KEY_ORG, KEY_EMAIL to appropriate value
. ./vars
./clean-all
./build-ca
On Windows:
vars
clean-all
build-ca
The final command (build-ca) will build the certificate authority (CA) certificate and key by invoking the interactive openssl command:
ai:easy-rsa # ./build-ca
Generating a 1024 bit RSA private key
…………++++++
………..++++++
writing new private key to ‘ca.key’
—–
Note that in the above sequence, most queried parameters were defaulted to the values set in the vars or vars.bat files. The only parameter which must be explicitly entered is the Common Name.
Generate certificate & key for server
Next, we will generate a certificate and private key for the server. On Linux/BSD/Unix:
./build-key-server server
On Windows:
build-key-server server
As in the previous step, most parameters can be defaulted. Two other queries require positive responses, “Sign the certificate? [y/n]” and “1 out of 1 certificate requests certified, commit? [y/n]“.
Generate certificates & keys for 3 clients
Generating client certificates is very similar to the previous step. On Linux/BSD/Unix:
./build-key client
On Windows:
build-key client1
If you would like to password-protect your client keys, substitute the build-key-pass script.
copy the dh1024.pem
ca.*
ta.*
server.crt & server.key to /etc/openvpn/gateway
client.crt & client.key to your client in /etc/openvpn/client
To verify the server certificate is valid, you can use the following:
Code:
openssl verify -CAfile ca.crt -purpose sslserver gateway.crt
To verify the client certiciate(s) is(are) valid, you can use the following:
Code:
openssl verify -CAfile ca.crt -purpose sslclient client.crt
Once you have all the configuration file in place, do the following on the server or Linux client.
Code:
/etc/init.d/openvpn start
You should now be able to ping the remote endpoints 10.22.8.1 and 10.22.8.10….
So that was the hardest part really. Making the VPN work :), now for the easy bit.
Routing PS3 traffic
What we want to do now is route all the traffic from the internal PS3 lan down the VPN and make the traffic go out to the USA PSN via the SERVER Internet access.
On the Linux client :-
echo “1″ > /proc/sys/net/ipv4/ip_forward # this allows routing over nics
iptables –table nat –append POSTROUTING –out-interface tap0 -j MASQUERADE
iptables –append FORWARD -s 172.16.0.2/24 -j ACCEPT
route add servervpninternetaddress netmask 255.255.255.255 your-internal-lan-ip-address
route del -net 0.0.0.0 gw your-internal-lan-ip-address
route add 0.0.0.0 gw 172.16.1.1
on the Linux Server :-
echo “1″ > /proc/sys/net/ipv4/ip_forward # this allows routing over nics
iptables –table nat –append POSTROUTING –out-interface eth0 -j MASQUERADE
iptables –append FORWARD –in-interface tap0 -j ACCEPT
On the PS3
Change the network settings
ip address : 172.16.0.2
mask : 255.255.255.0
def gw : 172.16.0.1
nameserver : 158.43.240.4
….
Reboot PS3 and thats is, youll be in the USA store
FINISH
So was haltet ihr davon ????

